You have probably heard of some high-profile network breaches in the news in recent months. Threat actors targeting organizations both large and small and have found success breaching secure environments using a technique called MFA spamming. This is a highly effective tactic because it targets the person, not the technology, to work around an organization’s MFA protections. Companies as large as Uber with highly sophisticated security programs have been targets of MFA Spamming attacks.
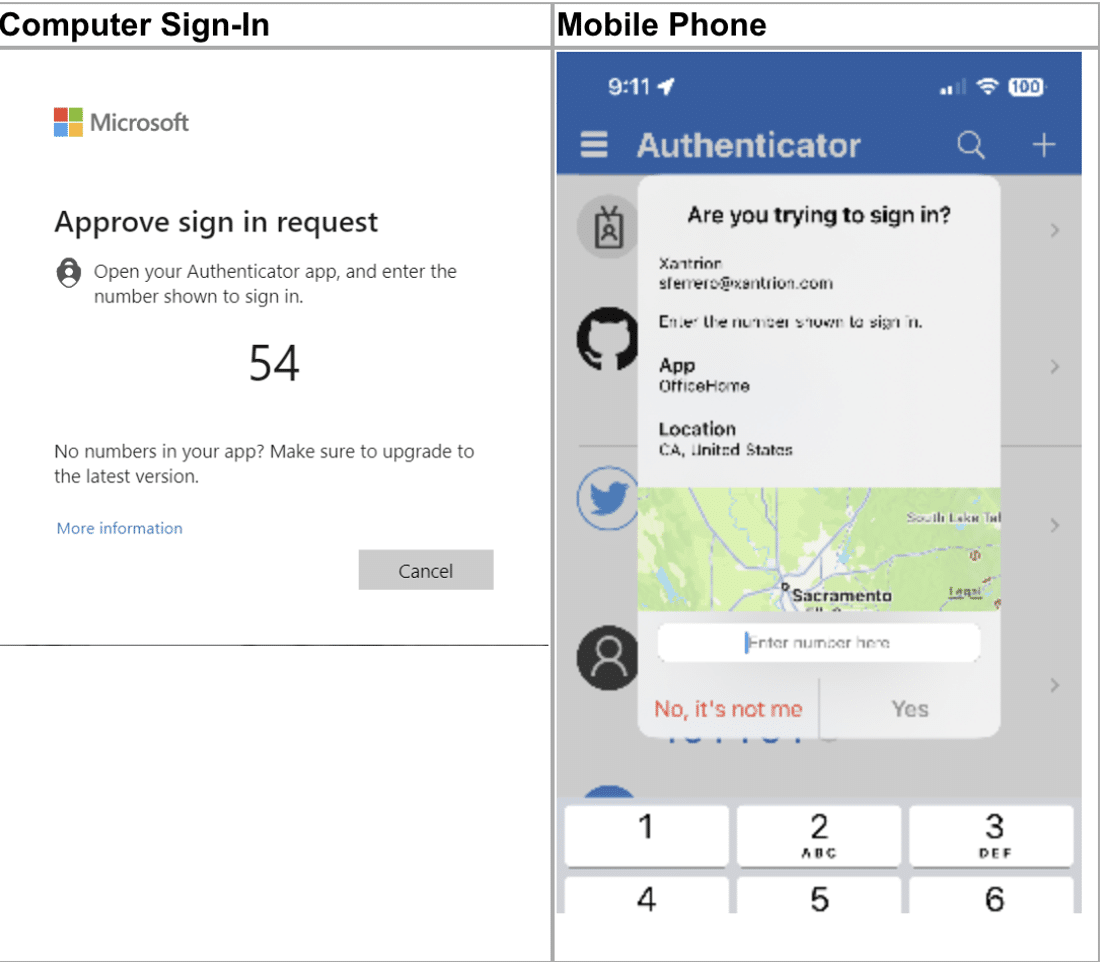
The updated Microsoft Authenticator will prompt you to enter a number displayed on the sign-in screen when approving an MFA request. This new experience protects you from the accidental approvals that make MFA spamming attacks work.
You will also notice location and application information displayed that can help determine if the MFA request was initiated by you. Below is an example of the new experience.
If your IT team isn’t talking about implementing this kind of more secure multi-factor authentication, we encourage you to ask about it, or contact us. We can help If you need a higher level of security, especially if you’re in a regulated industry and must demonstrate compliance or make use of many cloud services.